Workspace roles
In this article, you’ll learn how workspace roles work in Chromaport and how they affect user permissions.
Workspace roles define what a user can do across the entire workspace. Unlike computer permissions (which apply to specific machines), roles determine overall capabilities such as managing members, adding computers, or working with applications.
A user can have more than one role assigned, which expands their permissions and overall capabilities within the workspace.
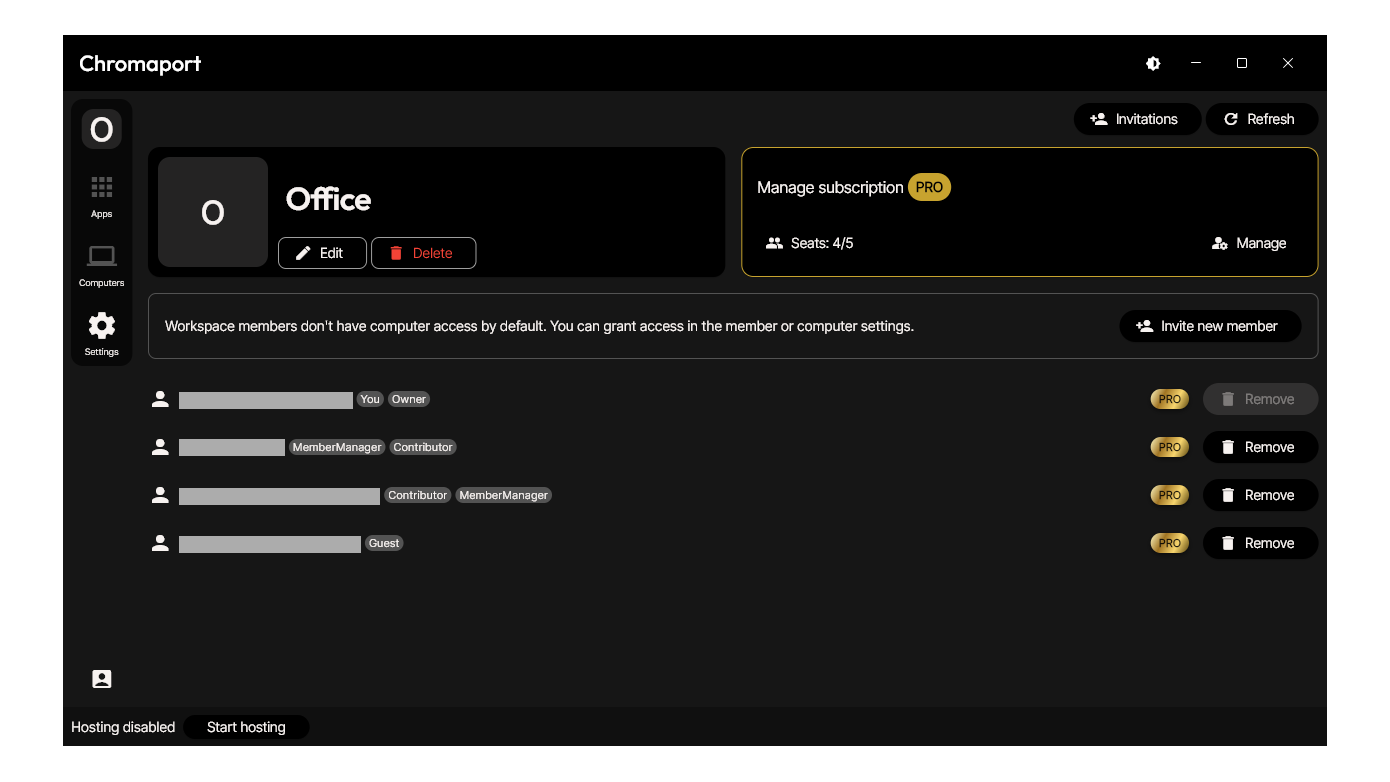
Roles are visible as tags next to each member, such as:
- Owner
- Contributor
- Member Manager
- Guest
Available roles
Owner
The Owner has full control over the workspace.
- Has all permissions combined
- Cannot be restricted or modified
- Always has full access to all computers
- Cannot be removed or unassigned
Contributor
A Contributor can actively work with computers and applications.
- Add computers
- Manage permissions of their own computers
- Add applications to the workspace
- Edit apps
Member Manager
Responsible for managing users.
- Invite members
- Remove members
- Edit member roles
Guest
Default role when no other roles are assigned.
- Limited access
- Permissions depend on assigned computers
Managing roles
You can manage roles in two ways:
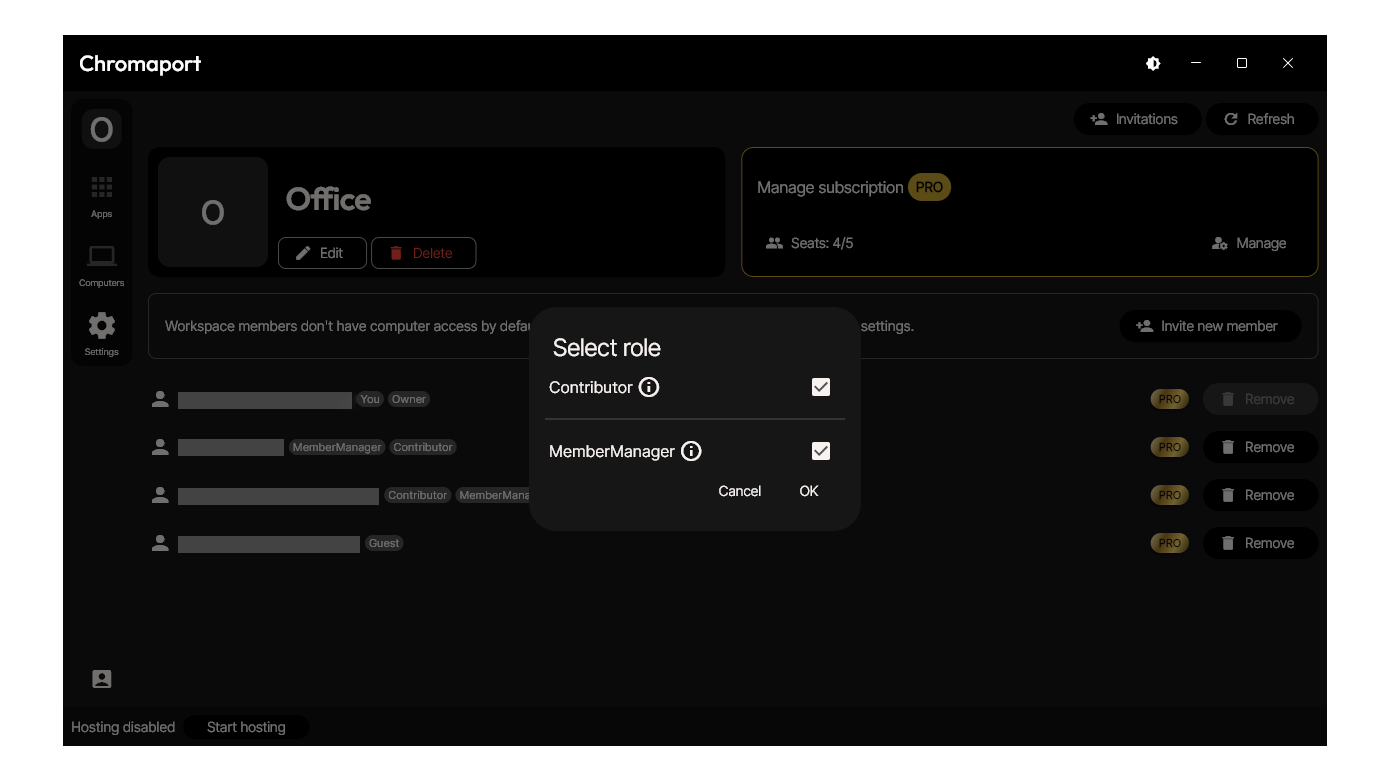
Using role tags
- Go to Settings
- Click on a role tag (e.g. Contributor, Member Manager, Guest) next to a member
- Enable or disable roles
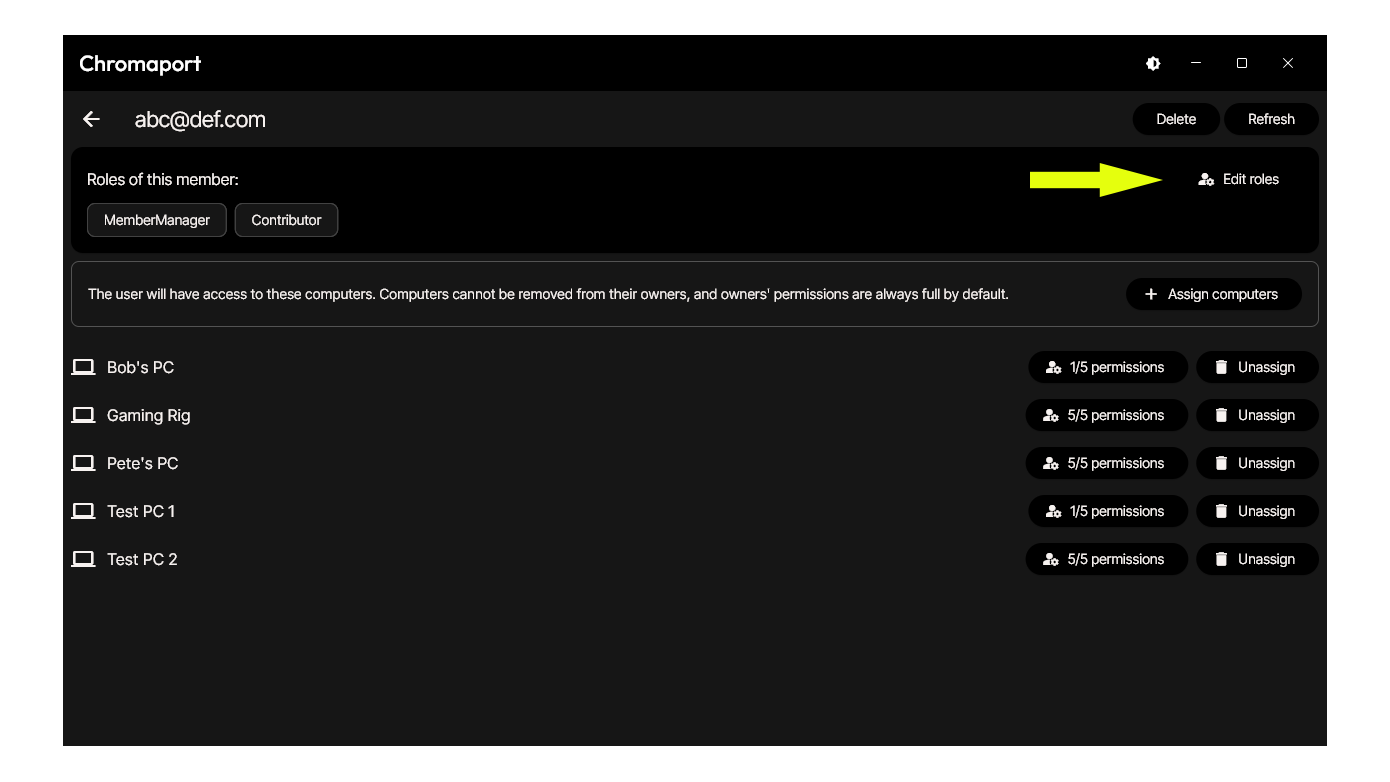
From member profile
- Go to Settings
- Select a user
- Click 'Edit roles' (top right)
- Assign or remove roles
Roles vs computer access
Workspace roles define general permissions, but they do not automatically grant access to computers.
For example:
- A user may be a Contributor
- But still won’t see or access any computer unless it is assigned to them
To manage access to specific machines, see the article: 'Computer permissions'.
Summary
Workspace roles control what users can do across your workspace, while computer permissions control what they can do on specific computers. Together, they create a flexible and secure access system for both individuals and teams.